There is a persistent gap between how seriously organisations talk about patch management and how rigorously they practise it. Most IT teams understand that keeping software up to date is important. Yet unpatched vulnerabilities remain one of the leading causes of successful cyberattacks year after year — not because the patches don’t exist, but because applying them consistently, at scale, and without disrupting operations is harder than it sounds.
Closing that gap is what effective patch management is really about.
What Patch Management Actually Involves
Patch management is the process of identifying, testing, deploying, and verifying software updates across an organisation’s environment. Those updates include security patches that fix known vulnerabilities, but also functional updates, bug fixes, and configuration changes that affect system stability and performance.
In a small environment, this might be manageable manually. In any organisation with dozens or hundreds of endpoints — running a mix of operating systems, third-party applications, and network devices — manual patching quickly becomes untenable. Updates need to be assessed for priority, tested to ensure they don’t break existing systems, deployed in the right sequence, and then verified to confirm successful installation. Doing this reliably, across an entire estate, without automation, is where most organisations run into trouble.
Why Unpatched Systems Are Such an Attractive Target
Attackers do not need to find novel vulnerabilities when known ones remain unpatched. Once a vulnerability is publicly disclosed and a patch is issued, that disclosure is effectively a roadmap for any attacker willing to scan for affected systems. Organisations that take weeks or months to apply critical patches are, during that window, exposed to threats that are already well-understood and actively exploited.
The scale of this problem is significant. Exploited vulnerabilities have ranked as the leading initial access vector in ransomware attacks for several consecutive years. Many of the most damaging incidents on record — including the WannaCry outbreak that affected hundreds of thousands of systems across 150 countries — succeeded not because organisations faced a zero-day they had no way to defend against, but because a patch that had already been released was never applied.
The window between vulnerability disclosure and active exploitation has also narrowed considerably. Researchers consistently find that attackers begin scanning for unpatched systems within hours of a patch being released — in some cases faster. An organisation with a 30-day patching cycle is exposed for far longer than the threat landscape now permits.
The Challenges Organisations Face
Understanding the importance of patching and executing it well are different problems. Several factors make consistent patch management genuinely difficult in practice.
Volume is the first challenge. The number of vulnerabilities disclosed each year runs into the thousands. Not all of them are equally critical, but identifying which patches to prioritise — and ensuring nothing significant slips through — requires structured processes and reliable tooling.
Compatibility creates friction. Patches occasionally break existing functionality, particularly in complex environments with legacy systems or heavily customised applications. The need to test before deploying at scale adds time to the process, which in turn extends the window of exposure.
Coverage is frequently incomplete. Organisations tend to patch operating systems reasonably well but fall behind on third-party applications — browsers, productivity tools, media players, PDF readers — which are among the most commonly exploited entry points. Devices that are rarely connected to the corporate network, or endpoints that fall outside standard management tools, can go unpatched indefinitely.
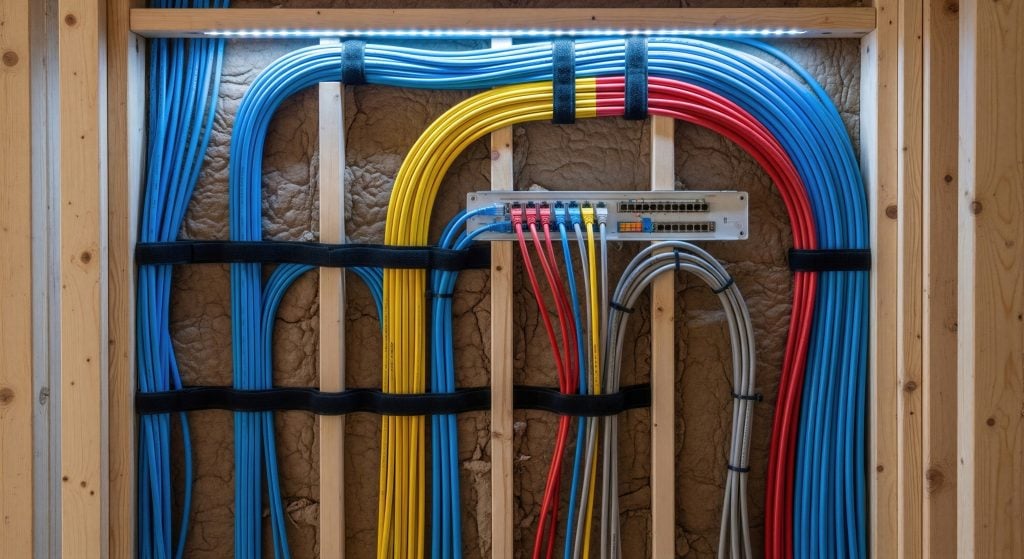
This is where dedicated patch management solutions make a material difference. Platforms like Heimdal’s provide automated discovery of installed software across the entire estate, continuous vulnerability scanning, and the ability to deploy patches silently and remotely — including to third-party applications that manual processes routinely miss. The result is a significant reduction in the time between patch availability and deployment, without the operational overhead of managing the process by hand.
Patch Management in the Context of Broader Security
Patch management does not exist in isolation. It is one layer in a defence-in-depth architecture — but it is a foundational one. DNS security, endpoint detection and response, and ransomware protection all become more effective when the vulnerabilities those controls are designed to protect are closed at the source.
An organisation that patches consistently reduces the attack surface that every other security control has to defend. Fewer unpatched vulnerabilities means fewer viable entry points, fewer successful exploits, and less work for detection and response tools to do downstream.
The Bottom Line
Patch management is not a glamorous discipline. It does not generate the same attention as threat detection or incident response. But in terms of measurable impact on an organisation’s exposure to attack, it is one of the most consequential things a security team can get right.
The organisations most likely to avoid a damaging breach are not necessarily those with the most sophisticated tools — they are the ones that execute the fundamentals consistently. Keeping systems patched is one of the most important of those fundamentals, and it is far more achievable than it often appears when the right processes and tooling are in place.
Sandra Larson is a writer with the personal blog at ElizabethanAuthor and an academic coach for students. Her main sphere of professional interest is the connection between AI and modern study techniques. Sandra believes that digital tools are a way to a better future in the education system.


![‘Parallel Tales’ Review – Asghar Farhadi’s Overlong But Potent Parasocial Fable [Cannes 2026] ‘Parallel Tales’ Review – Asghar Farhadi’s Overlong But Potent Parasocial Fable [Cannes 2026]](https://cdn.geekvibesnation.com/wp-media-folder-geek-vibes-nation/wp-content/uploads/2026/05/Parallel-Tales-Still-2-450x253.jpeg)


![‘Diamond’ Review – A Cinematic Love Letter To Authentic Detective Storytelling [Cannes 2026] ‘Diamond’ Review – A Cinematic Love Letter To Authentic Detective Storytelling [Cannes 2026]](https://cdn.geekvibesnation.com/wp-media-folder-geek-vibes-nation/wp-content/uploads/2026/05/Diamond-300x169.jpg)
